Advanced Threat Analytics (ATA)
Advanced Threat Analytics (ATA)
In our final blog post for this series, we will be discussing Advanced Threat Analytics (ATA), the final product in Enterprise Mobility + Security. The previous products have focused on protecting the user, the devices. With ATA, we cover the final piece of protecting the on-premises environment. ATA also takes us full circle because the best way to protect the on-premises environment is to again focus on protecting the users.
How is ATA different from other on-premises monitoring tools?
Most on-premises monitoring tools focus on the very visible threats that we are all used to hearing about and seeing in the environment – the CryptoLockers and the phishing links and so on. However, very few systems monitor for infections that work to stay hidden and are instead trying to gather company data and sensitive information for as long as possible. Many of these types of infections can stay hidden in networks for weeks or months before they are discovered, and that is what ATA is designed to eliminate.
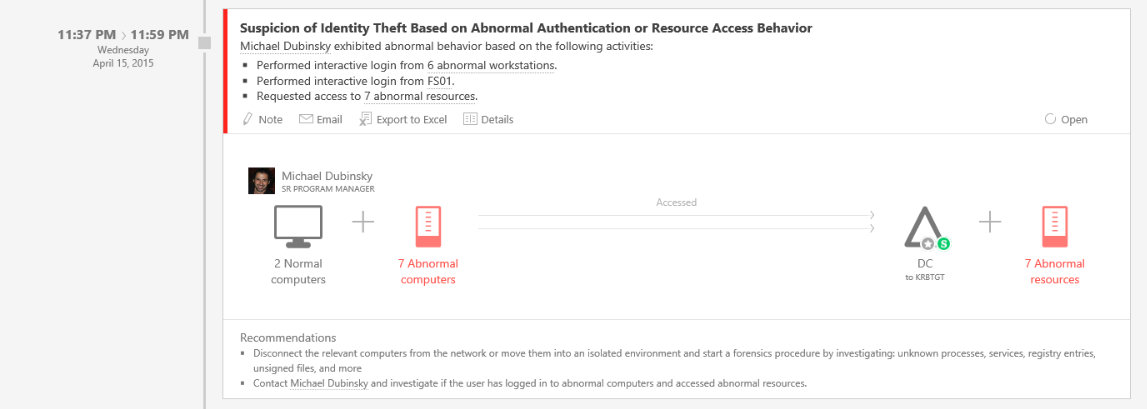
ATA focuses on the reality that any threat, regardless of how it manifests itself, needs a compromised user account to function. Because of this, ATA monitors and tracks all user authentication requests and user activity on the domain controllers and correlates that to known threats and questionable activity. ATA can then alert IT to these risks and allow the organization to respond appropriately to eliminate any threats or infections that might be in the environment.
ATA also brings Machine Learning and Risk-Based analysis to your on-premises Active Directory
In an earlier blog post, we discussed Risk Based Conditional Access and the ways in which it helps to secure logins to many applications. ATA brings that same machine learning and rule set to Active Directory as a whole and allows for detection of risks for on-premises users. Some of the common risk vectors that are detected include:
Impossible Travel
If a user authenticates to AD from Chicago and then signs in again 10 minutes later from Europe or Asia the system flags this as a risk. It would be impossible for the user to travel between those two locations in 10 minutes and so it is possible the account has been compromised.
Unusual Working Hours
Most employees work during a set period of hours. Even if they may work nights or weekends, their activity is usually fairly consistent. ATA will monitor and track login habits and if an employee who only ever logs in during the week all of a sudden logs in at 1 AM on a Sunday morning, ATA will flag that as anomalous so that the login can be verified as safe.
Abnormal Resource Access
Each user has a set list of systems and applications that they use on a regular basis. If at some point a user starts connecting to a large number of other systems for the first time, ATA will identify that activity and flag that account.
By using machine learning, Advanced Threat Analytics can not only detect the standard threats and malware but can also help to identify any compromised or questionable accounts and alert quickly so that the risk can be eliminated.
This wraps up our discussion of Enterprise Mobility + Security. As you can see there are a number of great products in this suite and we hope you have enjoyed this blog series. If you have any questions or would like a demo of any of these products please Contact BDO Digital. BDO Digital can develop a roadmap for an individualized strategy to keep your company secure and protected.


SHARE